What do you mean by a Firewall?
AfterAcademy Tech
•
10 Feb 2020

In today's world, most of the organization works on the internet. However, internet benefits come along with the risk involved with the internet. When the internet interacts with the organization it can be a threat to the organization itself. A firewall will reduce the exposure to external networks and host which poses a threat to the organization. It is the foundation from which the current network security technologies are built. So, let's get started and know more about the firewall.
Firewall
A firewall is a software program or a hardware device that acts as a filter for the data entering and leaving the network. The firewall can be analogous to the security guards who have control over who can enter or leave a building. A firewall reduces the risk and threat from the malicious packets that are travelling over the public network and can hamper the security of a private network.
How does a Firewall work?
A firewall acts as a border between your computer and the connected network(like LAN or internet). It inspects all the incoming and outgoing packets of the network. It inspects on the basis of programmed rules which are created by humans. These rules may depend on the demand, necessity and security policies defined by the organization. These rules will tell whether a packet will be allowed by the network barrier or not. If any packet is identified as a danger or threat according to the defined rules then it will not be allowed through the network. Though there are many rules and policies, the firewall also defines some default policies. It consists of three actions.
- Accept: Allows traffic to pass through.
- Drop: The network packages are dropped directly.
- Reject: It rejects or blocks the traffic. Additionally, it will reply with an error message.
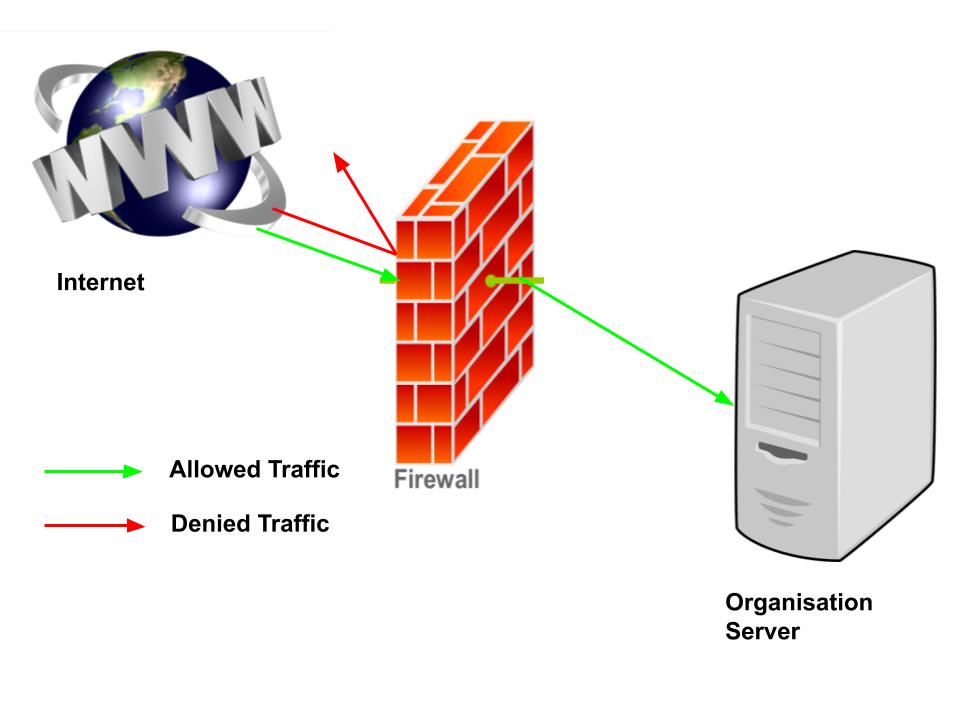
The firewall establishes a secured network and protects the internal network from the outside network or internet. In the above diagram, the firewall allows some traffic while it rejects malicious traffic.
Types of Firewall
- Packet-Filtering Firewalls: This is the oldest type of firewall architecture. When a packet passes through this firewall then it would check its source address, a destination address, port number, and protocols without opening the packet. If the packet is not according to the rules then the packet is dropped. These firewalls are of low cost and are best suited for small networks. However, these firewalls work only on the network layer and they are vulnerable to spoofing.
- Circuit-Level Gateway Firewalls: It works on the Session layer of the OSI model. It checks that the TCP 3-way handshakes are legitimate(according to the rules) or not. While they are extremely efficient but the firewall doesn't check the packet itself. So if any packet contains the malware and passes the TCP handshake checks then it would pass through the firewall and the system would be at risk.
- Stateful Inspection Firewalls: They are also called dynamic packet filtering firewalls. They maintain a track of all the open connections of the network. If any new packet arrives then the firewall checks if the new packet is of one the open connections then it simply allows the packet to pass. But, if the new packet is not of one of those open connections then it checks the packets according to the rules set for new connections.
- Application Firewall: It is also called a proxy-based firewall. This firewall operates at the application layer and filters the incoming traffic. When there is a proxy firewall then both the client and the server connect through an intermediary i.e. proxy servers. So, now when any external client wants to connect to any internal server or vice versa, then the client will have to open a connection with proxy instead. The proxy firewall first establishes a connection to the source of the traffic and then it inspects the incoming data packet. These firewalls may check the actual content of the packet so that if the packet contains any malware it can be rejected. The advantage of using a proxy server is that it makes hard for the attacker to discover a network actually is and hence provides security.
- Next-Generation Firewall: Most of the newly released firewalls are advertised as a next-generation architecture. Some of the common features of these firewalls are DataPacket Inspection(checking the actual content of the data), SSL/SSH Inspection(this secures you from HTTPs prone attacks), IPS(Intrusion Prevention System-this works to automatically stop the attack against your network). There is no proper definition of the Next-generation Firewall so one should check the capabilities of the firewall before buying one.
- Software Firewall: The software firewall may include any type of the above firewall that is installed on the local computer instead rather than a separate piece of hardware. It provides security as each individual network endpoint is isolated from others. Example: Windows Firewall is a software program that comes includes in Microsofts Windows.
- Hardware Firewall: Hardware Firewalls are the hardware devices which are found mostly on the routers. The hardware Firewall provides security from the malicious traffic from the outside networks as they are intercepted and blocked before they reach the internal network. Example: Cisco ASA 5540 series firewall

So, a firewall is important when
- You are surfing on the internet where you are using an ‘always on’ connection.
- You connect to an open Wi-Fi in a cafe, park, railway station, etc.
- Your organization needs to be isolated from the outside network.
- You want to know if any program on your system wants to connect to the internet.
This is was a brief discussion about the firewall. Hope you learned something new today.
Do share this blog with your friends to spread the knowledge. Visit our YouTube channel for more content. You can read more blogs from here.
Keep Learning 🙂
Team AfterAcademy!
Written by AfterAcademy Tech
Share this article and spread the knowledge
Read Similar Articles
AfterAcademy Tech
Difference between a Firewall and Antivirus
In this blog, we will learn about what is an antivirus and how does it work. We will then discuss the dissimilarities between the firewall and antivirus.
AfterAcademy Tech
What is the difference between SQL and MySQL?
In this blog, we will learn the difference between SQL and MySQL. People use these terms intechangeably. But both are having different meanings.